This is from the BlueHensCTF 2021.
For this challenge, we are given the following hint and file:

x = 2473, y = 1630, rule = B3/S23
2$
1406bo$
1407bo3bo$
1398b2o2b2o8bo12b2o$
1398b2o2bo5b2o2bo12b2o$
1402bobo5b2o$
1403b2o3b3o2$
1403b2o3b3o$
1402bobo5b2o$
1402bo5b2o2bo$
1402b2o8bo$
1407bo3bo$
1406bo2$
1435b2o$
1435b2o3$
1521bo$
1522bo3bo$
1513b2o2b2o8bo12b2o$
1513b2o2bo5b2o2bo12b2o$
1428b3o3b3o80bobo5b2o$
1428bo2bobo2bo81b2o3b3o$
1427bo3bobo3bo$
1427b4o3b4o80b2o3b3o$
1428bo7bo80bobo5b2o$
1517bo5b2o2bo$
1517b2o8bo$
1522bo3bo$
1521bo$
1427b$
1550b2o$
1435bo114b2o$
1434b3o$
1433bo3bo$
1433b2ob2o77bobo10b2o106bo$
1433b2ob2o77b2o11bobo106bo3bo$
1516bo11bo99b2o2b2o8bo12b2o$
1433b2ob2o190b2o2bo5b2o2bo12b2o$
1433b2ob2o105b3o3b3o80bobo5b2o$
1428b2o3bo3bo105bo2bobo2bo81b2o3b3o$
1428b2o4b3o105bo3bobo3bo$
1435bo106b4o3b4o80b2o3b3o$
1543bo7bo80bobo5b2o$
1632bo5b2o2bo$
1632b2o8bo$
1637bo3bo$
1539b3o94bo$
1539bo$
1540bo124b2o$
1550bo114b2o$
1549b3o$
1548bo3bo$
1548b2ob2o90b2o106bo$
1548b2ob2o90bobo106bo3bo$
1643bo99b2o2b2o8bo12b2o$
1548b2ob2o190b2o2bo5b2o2bo12b2o$
1548b2ob2o105b3o3b3o80bobo5b2o$
1492bobo48b2o3bo3bo105bo2bobo2bo81b2o3b3o$
1492b2o35b3o11b2o4b3o105bo3bobo3bo$
1493bo37bo18bo106b4o3b4o80b2o3b3o$
1530bo127bo7bo80bobo5b2o$
1747bo5b2o2bo$
1747b2o8bo$
1620bo131bo3bo$
1618b2o131bo$
1619b2o36b$
1780b2o$
1665bo114b2o$
1664b3o$
1663bo3bo$
1663b2ob2o198bo$
1663b2ob2o199bo3bo$
1858b2o2b2o8bo12b2o$
1663b2ob2o190b2o2bo5b2o2bo12b2o$
1663b2ob2o105b3o3b3o80bobo5b2o$
1658b2o3bo3bo105bo2bobo2bo81b2o3b3o$
1658b2o4b3o105bo3bobo3bo$
1665bo106b4o3b4o80b2o3b3o$
1773bo7bo80bobo5b2o$
1862bo5b2o2bo$
1862b2o8bo$
1867bo3bo$
1866bo$
1772b$
1895b2o$
1780bo114b2o$
1779b3o$
1778bo3bo$
1778b2ob2o198bo$
1778b2ob2o199bo3bo$
1973b2o2b2o8bo12b2o$
1778b2ob2o190b2o2bo5b2o2bo12b2o$
1778b2ob2o105b3o3b3o80bobo5b2o$
1773b2o3bo3bo105bo2bobo2bo81b2o3b3o$
1773b2o4b3o105bo3bobo3bo$
1780bo106b4o3b4o80b2o3b3o$
1888bo7bo80bobo5b2o$
1977bo5b2o2bo$
1977b2o8bo$
1621b3o226bo131bo3bo$
1623bo224b2o131bo$
1622bo226b2o36b$
2010b2o$
1446bobo446bo114b2o$
1446b2o35b3o408b3o$
1447bo37bo262b2o143bo3bo$
1484bo262bobo143b2ob2o198bo$
1749bo143b2ob2o199bo3bo$
2088b2o2b2o8bo12b2o$
1574bo318b2ob2o190b2o2bo5b2o2bo12b2o$
1572b2o319b2ob2o105b3o3b3o80bobo5b2o$
1573b2o313b2o3bo3bo105bo2bobo2bo81b2o3b3o$
1874b3o11b2o4b3o105bo3bobo3bo$
1876bo18bo106b4o3b4o80b2o3b3o$
1875bo127bo7bo80bobo5b2o$
1472b2o618bo5b2o2bo$
1471bobo225bobo390b2o8bo$
1473bo225b2o396bo3bo$
1700bo395bo$
2002b$
2125b2o$
2010bo114b2o$
2009b3o$
1863b2o143bo3bo$
1862bobo143b2ob2o77bobo118bo$
1864bo143b2ob2o77b2o120bo3bo$
2091bo111b2o2b2o8bo12b2o$
1460b3o545b2ob2o190b2o2bo5b2o2bo12b2o$
1462bo545b2ob2o105b3o3b3o80bobo5b2o$
1461bo490bobo48b2o3bo3bo105bo2bobo2bo81b2o3b3o$
1952b2o49b2o4b3o105bo3bobo3bo$
1953bo56bo106b4o3b4o80b2o3b3o$
1551bo566bo7bo80bobo5b2o$
1549b2o656bo5b2o2bo$
1550b2o655b2o8bo$
1851b3o358bo3bo$
1853bo357bo$
1852bo264b$
2240b2o$
1676bobo446bo114b2o$
1676b2o446b3o$
1677bo300b2o143bo3bo$
1977bobo143b2ob2o77bobo10b2o106bo$
1979bo143b2ob2o77b2o11bobo106bo3bo$
2206bo11bo99b2o2b2o8bo12b2o$
1575b3o545b2ob2o190b2o2bo5b2o2bo12b2o$
1577bo262b2o281b2ob2o105b3o3b3o80bobo5b2o$
1576bo262bobo276b2o3bo3bo105bo2bobo2bo81b2o3b3o$
1841bo276b2o4b3o105bo3bobo3bo$
2125bo106b4o3b4o80b2o3b3o$
2233bo7bo80bobo5b2o$
1702b2o618bo5b2o2bo$
1701bobo618b2o8bo$
1703bo262b3o358bo3bo$
1968bo357bo$
1967bo264b$
2355b2o$
2240bo114b2o$
2239b3o$
2093b2o143bo3bo$
2092bobo143b2ob2o198bo$
1426b2o666bo143b2ob2o199bo3bo$
1425bobo1005b2o2b2o8bo12b2o$
1427bo810b2ob2o190b2o2bo5b2o2bo12b2o$
2238b2ob2o105b3o3b3o80bobo5b2o$
2233b2o3bo3bo105bo2bobo2bo81b2o3b3o$
2219b3o11b2o4b3o105bo3bobo3bo$
2221bo18bo106b4o3b4o80b2o3b3o$
2220bo127bo7bo80bobo5b2o$
2437bo5b2o2bo$
2437b2o8bo$
2442bo3bo$
2441bo$
1414b3o930b$
1416bo1053b2o$
1415bo490bobo446bo114b2o$
1906b2o446b3o$
1907bo445bo3bo$
1505bo847b2ob2o93b$
1503b2o848b2ob2o93b$
1504b2o945b$
2353b2ob2o$
2353b2ob2o105b3o3b3o$
2348b2o3bo3bo105bo2bobo2bo$
1403b2o943b2o4b3o105bo3bobo3bo$
1402bobo225bobo722bo106b4o3b4o$
1404bo225b2o831bo7bo$
1631bo302b$
2162b$
2426b$
2462b$
1529b3o226bo703b$
1531bo224b2o36b2o666b$
1530bo226b2o34bobo674bo$
1795bo673b3o$
2468bo3bo$
1391b3o1074b2ob2o$
1393bo1074b2ob2o$
1392bo493b$
1920b3o226bo318b2ob2o$
1922bo224b2o36b2o281b2ob2o$
1921bo226b2o34bobo276b2o3bo3bo$
2186bo276b2o4b3o$
2470bo$
2011bo440b$
2009b2o36b2o$
2010b2o34bobo228b$
1380b2o666bo265b$
1379bobo225bobo704b$
1381bo225b2o705b$
1608bo302b$
2139b$
2403b$
2440b$
1735bo704b$
1733b2o705b$
1734b2o265b$
2265b$
2302b$
2302b$
2302b$
1863b$
2127b$
2164b$
2392b$
2426b3o$
2428bo$
2427bo$
2026b$
2254b$
1357b2o932b$
1356bobo932b$
1358bo262b3o667b$
1623bo264b$
1622bo493b$
2150b3o227b$
2152bo262b2o$
2151bo262bobo$
1748b2o666bo$
1747bobo228b$
1749bo262b3o227b$
2014bo264b$
1345b3o665bo265b$
1347bo931b$
1346bo493b$
1874b3o227b$
1876bo262b2o$
1875bo262bobo228b$
2140bo265b$
2406b$
1965bo440b$
1963b2o38b$
1964b2o265b$
1334b2o932b$
1333bobo225bobo704b$
1335bo225b2o705b$
1562bo302b$
2093b$
2127b3o227b$
2129bo264b$
1689bo438bo265b$
1687b2o705b$
1688b2o265b$
1989b3o226bo$
1991bo224b2o38b$
1322b3o665bo226b2o37b$
1324bo262b2o667b$
1323bo262bobo225bobo$
1588bo225b2o265b$
1815bo302b$
2346b$
1449b2o932b$
1448bobo932b$
1450bo932b$
1980b$
2205bobo$
1311b2o892b2o38b$
1310bobo893bo38b$
1312bo262b3o667b$
1577bo262b2o$
1576bo262bobo225bobo$
1841bo225b2o265b$
2068bo302b$
1437b3o226bo704b$
1439bo224b2o36b2o667b$
1438bo226b2o34bobo228b$
1703bo492b$
2231b2o$
2230bobo$
1564b2o666bo$
1563bobo225bobo$
1565bo225b2o265b$
1792bo302b$
2323b$
2360b$
2360b$
1919bo440b$
1917b2o38b$
1918b2o265b$
2222b$
2222b$
1552b3o667b$
1554bo264b$
1553bo493b$
2081b3o227b$
2083bo264b$
2082bo265b$
2348b$
1909b$
1943b3o227b$
1945bo264b$
1944bo265b$
2210b$
1771b$
2035b$
2070b2o$
2069bobo228b$
1403b2o666bo265b$
1402bobo932b$
1404bo262b3o667b$
1669bo264b$
1668bo493b$
2199b$
2199b$
1529b3o667b$
1531bo264b$
1530bo490bobo$
2021b2o35b3o227b$
2022bo37bo264b$
1620bo438bo265b$
1618b2o705b$
1619b2o265b$
1920b3o227b$
1922bo264b$
1921bo265b$
1518b2o667b$
1517bobo225bobo$
1519bo225b2o265b$
1746bo302b$
2277b$
2314b$
2314b$
1873bo440b$
1871b2o38b$
1872b2o265b$
2176b$
2176b$
1506b3o667b$
1508bo262b2o$
1507bo262bobo228b$
1772bo262b3o227b$
1331bobo703bo264b$
1331b2o703bo265b$
1332bo969b$
1863b$
2127b$
2164b$
1230b3o931b$
1232bo931b$
1231bo490bobo$
1722b2o265b$
1723bo300b2o$
1321bo701bobo228b$
1319b2o36b2o666bo265b$
1320b2o34bobo932b$
1358bo262b3o226bo440b$
1623bo224b2o36b2o$
1622bo226b2o34bobo228b$
1887bo265b$
2153b$
2153b$
1748b2o$
1747bobo228b$
1749bo262b3o227b$
2014bo264b$
2013bo265b$
1610b2o667b$
1609bobo228b$
1611bo492b$
2141b$
2141b$
2141b$
1702b$
1965bo$
1963b2o36b2o$
1964b2o34bobo228b$
2002bo265b$
2268b$
2268b$
1865b$
2093b$
2130b$
2130b$
2130b$
1727b$
1952bobo$
1952b2o35b3o227b$
1953bo37bo264b$
1990bo265b$
2256b$
1817b$
2081b$
2118b$
1184b3o931b$
1186bo931b$
1185bo490bobo$
1676b2o35b3o226bo$
1677bo37bo224b2o38b$
1714bo226b2o265b$
2245b$
2245b$
1575b3o226bo440b$
1577bo224b2o38b$
1576bo226b2o265b$
2107b$
2107b$
2107b$
1704b$
1932b$
2196b$
2233b$
1299b3o931b$
1301bo931b$
1300bo493b$
2058b$
2095b$
1390bo704b$
1388b2o36b2o667b$
1389b2o34bobo228b$
1427bo492b$
1955b2o$
1954bobo228b$
1956bo265b$
2222b$
1781bo440b$
1779b2o38b$
1114bo665b2o265b$
1112b2o970b$
1113b2o969b$
2084b$
1681b$
1909b$
1943b3o227b$
1945bo264b$
1944bo265b$
1541b2o667b$
1540bobo228b$
1542bo492b$
1101bobo968b$
1101b2o969b$
1102bo300b2o667b$
1402bobo228b$
1404bo491bo$
1894b2o36b2o$
1895b2o34bobo228b$
1933bo265b$
2199b$
2199b$
1794b2o$
1091bo701bobo228b$
1089b2o704bo265b$
1090b2o262bobo704b$
1354b2o705b$
1355bo302b$
1883bobo$
1883b2o265b$
1884bo302b$
1253b3o931b$
1255bo931b$
1254bo493b$
2012b$
2049b$
1115b3o226bo704b$
1117bo224b2o705b$
1116bo226b2o265b$
1873bo$
1871b2o38b$
1872b2o265b$
2176b$
2176b$
1735bo440b$
1733b2o38b$
1734b2o265b$
1104b2o932b$
1103bobo225bobo704b$
1105bo225b2o35b3o667b$
1332bo37bo264b$
1369bo490bobo$
1860b2o265b$
1861bo302b$
2164b$
2164b$
1725b$
1989b$
2026b$
1092b3o931b$
1094bo931b$
1093bo493b$
1621b3o227b$
1623bo264b$
1183bo438bo493b$
1181b2o970b$
1182b2o262bobo704b$
1446b2o705b$
1447bo302b$
1978b$
2015b$
2015b$
2015b$
1612b$
1840b$
1874b3o227b$
1876bo264b$
1875bo265b$
2141b$
1702b$
1966b$
2003b$
1298bo704b$
1296b2o705b$
1297b2o265b$
1827bo$
1825b2o38b$
1826b2o265b$
2130b$
2130b$
2130b$
1727b$
1022bo932b$
1020b2o970b$
1021b2o262bobo704b$
1285b2o705b$
1286bo302b$
1814bobo$
1814b2o265b$
1815bo302b$
2118b$
1449b2o667b$
1448bobo228b$
1450bo492b$
1980b$
1980b$
1980b$
1541b$
1804bo$
1802b2o36b2o$
1137bo665b2o34bobo228b$
1135b2o704bo265b$
1136b2o969b$
2107b$
1702b2o$
1701bobo228b$
1703bo265b$
1262bobo704b$
1262b2o705b$
1263bo300b2o$
1563bobo228b$
1565bo492b$
2095b$
2095b$
2095b$
1656b$
1920b$
1957b$
1957b$
1957b$
1515bobo$
1515b2o35b3o227b$
1516bo37bo262b2o$
1553bo262bobo228b$
1818bo265b$
1377bobo704b$
1377b2o705b$
1378bo302b$
1909b$
1946b$
1239bobo704b$
1239b2o264bo440b$
1240bo262b2o36b2o$
1504b2o34bobo228b$
1542bo492b$
2072b$
2072b$
2072b$
1633b$
1667b3o227b$
1669bo264b$
1668bo265b$
1265b2o667b$
1264bobo228b$
1266bo262b3o227b$
1531bo262b2o$
1530bo262bobo228b$
1795bo265b$
2061b$
1391b3o667b$
1393bo264b$
1392bo493b$
1923b$
1923b$
1253b3o667b$
1255bo262b2o$
1254bo262bobo228b$
1519bo262b3o227b$
1078bobo703bo264b$
1078b2o703bo265b$
1079bo969b$
1610b$
1644b3o227b$
1646bo264b$
1645bo265b$
1242b2o667b$
1241bobo228b$
1243bo492b$
1771b2o$
1770bobo228b$
1772bo265b$
1331bobo704b$
1331b2o705b$
1332bo302b$
1863b$
1900b$
1900b$
1459bo440b$
1457b2o36b2o$
1458b2o34bobo228b$
1496bo262b3o227b$
1761bo264b$
1321bo438bo265b$
1319b2o36b2o667b$
1320b2o34bobo228b$
1358bo492b$
1888b$
1888b$
1888b$
1446bobo$
1446b2o265b$
1447bo300b2o$
1747bobo228b$
1749bo265b$
2015b$
2015b$
1612b$
1840b$
1877b$
1877b$
1207b3o667b$
1209bo262b2o$
1208bo262bobo228b$
1473bo492b$
2003b$
2003b$
2003b$
1561bobo$
1561b2o265b$
1562bo302b$
1160bo704b$
1158b2o705b$
1159b2o265b$
1690b$
1727b$
1955b$
1992b$
1285bobo704b$
1285b2o35b3o667b$
1286bo37bo264b$
1323bo493b$
1854b$
1147bobo704b$
1147b2o35b3o667b$
1148bo37bo264b$
1185bo493b$
1943b$
1980b$
1275bo704b$
1273b2o705b$
1274b2o265b$
1805b$
1842b$
1137bo704b$
1135b2o705b$
1136b2o265b$
1667b$
1702b2o$
1701bobo228b$
1703bo265b$
1969b$
1299b3o226bo440b$
1301bo224b2o38b$
1300bo226b2o265b$
1831b$
1831b$
1831b$
1428b$
1656b$
1690b3o227b$
1692bo264b$
1023b3o665bo265b$
1025bo931b$
1024bo493b$
1782b$
1819b$
1114bo704b$
1112b2o36b2o667b$
1113b2o34bobo225bobo$
1151bo225b2o265b$
1378bo302b$
1909b$
1012b2o932b$
1011bobo932b$
1013bo932b$
1541b2o$
1540bobo228b$
1542bo265b$
1101bobo704b$
1101b2o705b$
1102bo302b$
1633b$
1667b3o227b$
1669bo264b$
1229bo438bo265b$
1227b2o705b$
1228b2o265b$
1759b$
1796b$
1091bo704b$
1089b2o36b2o667b$
1090b2o34bobo225bobo$
1128bo225b2o264bo$
1355bo262b2o38b$
1619b2o265b$
1923b$
1923b$
1923b$
1520b$
1748b$
1785b$
1785b$
1785b$
1382b$
1610b$
1874b$
1911b$
977b3o931b$
979bo931b$
978bo493b$
1736b$
1773b$
839b3o931b$
841bo931b$
840bo493b$
1368b3o227b$
1370bo262b2o$
1369bo262bobo228b$
1634bo265b$
1193bobo704b$
1193b2o705b$
1194bo300b2o$
1494bobo228b$
1496bo265b$
1762b$
1762b$
1359b$
1587b$
1851b$
1888b$
954b3o931b$
956bo931b$
955bo493b$
1713b$
1750b$
1045bo704b$
1043b2o705b$
1044b2o265b$
1574bo$
1572b2o38b$
1573b2o265b$
1877b$
1877b$
1436bo440b$
1434b2o38b$
1435b2o265b$
805b2o932b$
804bobo225bobo704b$
806bo225b2o705b$
1033bo302b$
1561bobo$
1561b2o35b3o227b$
1562bo37bo264b$
1599bo265b$
1196b2o667b$
1195bobo228b$
1197bo262b3o227b$
1462bo264b$
1022bo438bo265b$
1020b2o705b$
1021b2o262bobo$
1285b2o35b3o226bo$
1286bo37bo224b2o36b2o$
1323bo226b2o34bobo228b$
1588bo265b$
1854b$
1413bo440b$
1411b2o38b$
1412b2o262bobo$
782b2o892b2o38b$
781bobo893bo38b$
783bo932b$
1313b$
1541b$
1575b3o227b$
1577bo264b$
1137bo438bo265b$
1135b2o705b$
1136b2o265b$
1437b3o226bo$
1439bo224b2o38b$
1438bo226b2o37b$
1035b2o667b$
1034bobo228b$
1036bo492b$
1564b2o$
1563bobo228b$
1565bo265b$
1831b$
1831b$
1428b$
1656b$
1693b$
1693b$
1023b3o226bo440b$
1025bo224b2o36b2o$
1024bo226b2o34bobo228b$
1289bo492b$
1819b$
1819b$
1150b2o667b$
1149bobo228b$
1151bo492b$
1681b$
976bo704b$
974b2o36b2o667b$
975b2o34bobo228b$
1013bo492b$
1541b2o$
1540bobo228b$
1542bo265b$
1101bobo704b$
1101b2o264bo440b$
1102bo262b2o38b$
1366b2o265b$
1670b$
1670b$
1000b3o667b$
1002bo262b2o$
1001bo262bobo225bobo$
1266bo225b2o265b$
1493bo302b$
1796b$
1796b$
1357b$
1621b$
1658b$
953bo704b$
951b2o705b$
952b2o262bobo$
1216b2o35b3o227b$
1217bo37bo262b2o$
1254bo262bobo228b$
851b2o666bo265b$
850bobo932b$
852bo262b3o226bo440b$
1117bo224b2o38b$
1116bo226b2o265b$
1647b$
940bobo704b$
940b2o35b3o226bo440b$
941bo37bo224b2o36b2o$
978bo226b2o34bobo228b$
1243bo492b$
1773b$
1068bo704b$
1066b2o705b$
1067b2o265b$
1368b3o227b$
1370bo264b$
1369bo265b$
966b2o667b$
965bobo228b$
967bo262b3o226bo$
1232bo224b2o36b2o$
1231bo226b2o34bobo228b$
1496bo265b$
1762b$
1092b3o667b$
1094bo264b$
1093bo493b$
1624b$
917bobo704b$
917b2o35b3o667b$
918bo37bo262b2o$
955bo262bobo225bobo$
1220bo225b2o265b$
1447bo302b$
1045bo704b$
1043b2o705b$
1044b2o262bobo$
1308b2o35b3o227b$
1309bo37bo264b$
678b3o226bo438bo265b$
680bo224b2o705b$
679bo226b2o265b$
1436bo$
1434b2o36b2o$
1435b2o34bobo228b$
805b2o666bo265b$
804bobo932b$
806bo932b$
1336b$
1564b$
1601b$
894bobo704b$
894b2o264bo440b$
895bo262b2o36b2o$
1159b2o34bobo228b$
1197bo262b3o227b$
1462bo264b$
1022bo438bo265b$
1020b2o705b$
1021b2o262bobo$
1285b2o35b3o227b$
1286bo37bo264b$
1323bo265b$
1589b$
1150b$
1414b$
1449b2o$
1448bobo228b$
1450bo265b$
1716b$
1046b3o667b$
1048bo264b$
608bo438bo493b$
606b2o970b$
607b2o969b$
908b3o667b$
910bo262b2o$
470bo438bo262bobo225bobo$
468b2o704bo225b2o265b$
469b2o930bo302b$
999bo704b$
997b2o705b$
998b2o265b$
1529b$
1566b$
632b3o931b$
634bo262b2o667b$
633bo262bobo225bobo$
898bo225b2o265b$
457bobo665bo302b$
457b2o1197b$
458bo1234b$
1693b$
1023b3o667b$
1025bo264b$
1024bo493b$
1555b$
1555b$
885b3o667b$
887bo262b2o$
886bo262bobo228b$
1151bo492b$
1681b$
1681b$
1681b$
1242b$
1506b$
1543b$
1543b$
1543b$
1101bobo$
1101b2o264bo$
1102bo262b2o36b2o$
1366b2o34bobo228b$
1404bo265b$
1670b$
1000b3o667b$
1002bo262b2o$
1001bo262bobo228b$
1266bo265b$
1532b$
1532b$
1129b$
1357b$
1391b3o227b$
1393bo264b$
1392bo265b$
1658b$
1216bobo$
1216b2o265b$
549bobo665bo302b$
549b2o969b$
550bo300b2o667b$
850bobo225bobo$
852bo225b2o35b3o227b$
1079bo37bo262b2o$
1116bo262bobo228b$
1381bo265b$
940bobo704b$
940b2o35b3o667b$
941bo37bo262b2o$
978bo262bobo228b$
1243bo265b$
1509b$
839b3o667b$
841bo262b2o$
840bo262bobo225bobo$
1105bo225b2o265b$
664bobo665bo302b$
664b2o969b$
665bo969b$
1196b$
1460b$
1497b$
792bo704b$
790b2o705b$
791b2o262bobo$
1055b2o264bo$
1056bo262b2o38b$
654bo665b2o265b$
652b2o970b$
653b2o969b$
954b3o226bo440b$
956bo224b2o38b$
955bo226b2o265b$
1486b$
779bobo704b$
779b2o35b3o667b$
780bo37bo264b$
817bo490bobo$
1308b2o35b3o227b$
1309bo37bo264b$
1346bo265b$
1612b$
1173b$
1437b$
503bobo968b$
503b2o264bo704b$
504bo262b2o705b$
768b2o265b$
1299b$
1336b$
1564b$
1601b$
1601b$
1160bo440b$
1158b2o36b2o$
1159b2o34bobo228b$
1197bo265b$
1463b$
1022bo440b$
1020b2o38b$
1021b2o262bobo$
1285b2o265b$
1286bo302b$
1589b$
1589b$
1150b$
1414b$
1451b$
1451b$
1451b$
1009bobo$
1009b2o264bo$
1010bo262b2o38b$
608bo665b2o265b$
606b2o970b$
607b2o969b$
1137bo440b$
1135b2o36b2o$
1136b2o34bobo228b$
1174bo265b$
1440b$
770b3o667b$
772bo264b$
771bo490bobo$
1262b2o35b3o227b$
1263bo37bo264b$
1300bo265b$
1566b$
1127b$
1391b$
1428b$
723bo704b$
721b2o36b2o667b$
722b2o34bobo228b$
760bo262b3o226bo$
1025bo224b2o38b$
1024bo226b2o265b$
1555b$
848bobo704b$
848b2o264bo440b$
849bo262b2o38b$
1113b2o265b$
1417b$
1417b$
747b3o667b$
749bo264b$
748bo493b$
1506b$
1543b$
1543b$
874b2o667b$
873bobo228b$
875bo262b3o227b$
1140bo264b$
700bo438bo265b$
698b2o705b$
699b2o265b$
1000b3o227b$
1002bo264b$
562bo438bo493b$
560b2o970b$
561b2o969b$
862b3o226bo440b$
864bo224b2o38b$
863bo226b2o265b$
1394b$
1394b$
1394b$
991b$
1216bobo$
1216b2o265b$
1217bo302b$
815bo704b$
813b2o705b$
814b2o265b$
1115b3o227b$
1117bo264b$
1116bo265b$
1382b$
943b$
1207b$
1242b2o$
1241bobo228b$
1243bo265b$
1509b$
1509b$
1106b$
1334b$
1371b$
664bobo704b$
664b2o705b$
665bo300b2o$
965bobo225bobo$
967bo225b2o35b3o227b$
1194bo37bo264b$
1231bo265b$
828b2o667b$
827bobo228b$
829bo492b$
1359b$
1359b$
1359b$
920b$
1184b$
1219b2o$
1218bobo228b$
552b2o666bo265b$
551bobo225bobo704b$
553bo225b2o705b$
780bo300b2o$
1080bobo228b$
1082bo265b$
641bobo704b$
641b2o35b3o226bo440b$
642bo37bo224b2o36b2o$
679bo226b2o34bobo225bobo$
944bo225b2o35b3o227b$
1171bo37bo264b$
1208bo265b$
805b2o667b$
804bobo228b$
806bo492b$
1336b$
631bo704b$
629b2o705b$
630b2o265b$
1161b$
1198b$
1426b$
1463b$
1463b$
1463b$
1060b$
1288b$
1325b$
618bobo704b$
618b2o35b3o667b$
619bo37bo264b$
656bo493b$
1184b3o227b$
1186bo264b$
746bo438bo265b$
744b2o705b$
745b2o265b$
1276b$
1313b$
608bo704b$
606b2o705b$
607b2o262bobo$
871b2o35b3o226bo$
872bo37bo224b2o36b2o$
909bo226b2o34bobo228b$
506b2o666bo265b$
505bobo932b$
507bo932b$
1037b$
1265b$
368b2o932b$
367bobo932b$
369bo262b3o667b$
634bo262b2o$
633bo262bobo225bobo$
898bo225b2o35b3o227b$
1125bo37bo264b$
723bo438bo265b$
721b2o36b2o667b$
722b2o34bobo228b$
760bo492b$
1290b$
356b3o931b$
358bo931b$
357bo490bobo$
848b2o35b3o226bo$
849bo37bo224b2o38b$
886bo226b2o265b$
483b2o932b$
482bobo932b$
484bo932b$
1014b$
1242b$
345b2o932b$
344bobo932b$
346bo491bo440b$
836b2o36b2o$
837b2o34bobo228b$
875bo492b$
1405b$
1405b$
736b2o667b$
735bobo225bobo$
737bo225b2o265b$
296bobo665bo302b$
296b2o969b$
297bo969b$
825bobo$
825b2o35b3o226bo$
826bo37bo224b2o36b2o$
863bo226b2o34bobo228b$
1128bo265b$
1394b$
1394b$
991b$
1219b$
1256b$
1256b$
586b3o226bo440b$
588bo224b2o38b$
587bo226b2o262bobo$
1078b2o35b3o227b$
1079bo37bo264b$
677bo438bo265b$
675b2o705b$
676b2o265b$
977b3o227b$
979bo264b$
310b3o665bo265b$
312bo931b$
311bo490bobo$
802b2o264bo$
803bo262b2o36b2o$
1067b2o34bobo228b$
1105bo265b$
1371b$
930bo440b$
928b2o38b$
929b2o265b$
1233b$
1233b$
1233b$
828b2o$
827bobo225bobo$
829bo225b2o35b3o227b$
1056bo37bo264b$
1093bo265b$
690b2o667b$
689bobo228b$
691bo492b$
250bobo968b$
250b2o969b$
251bo300b2o667b$
551bobo225bobo$
553bo225b2o35b3o226bo$
780bo37bo224b2o36b2o$
817bo226b2o34bobo228b$
1082bo265b$
1348b$
1348b$
945b$
1173b$
1210b$
503bobo704b$
503b2o35b3o667b$
504bo37bo264b$
541bo493b$
1299b$
1336b$
1336b$
667b2o667b$
666bobo225bobo$
668bo225b2o265b$
895bo302b$
493bo704b$
491b2o36b2o667b$
492b2o34bobo228b$
530bo491bo$
1020b2o38b$
355bo665b2o265b$
353b2o970b$
354b2o969b$
1325b$
922b$
1150b$
1187b$
480bobo704b$
480b2o705b$
481bo302b$
1009bobo$
1009b2o265b$
1010bo302b$
1313b$
1313b$
874b$
1138b$
1175b$
1175b$
1175b$
733bobo$
733b2o264bo$
734bo262b2o36b2o$
998b2o34bobo228b$
1036bo265b$
1302b$
1302b$
899b$
1127b$
1164b$
1164b$
1164b$
761b$
989b$
1023b3o227b$
1025bo264b$
1024bo265b$
1290b$
851b$
1115b$
1152b$
1152b$
483b2o667b$
482bobo228b$
484bo492b$
1014b$
309bo932b$
307b2o970b$
8b2o298b2o262bobo704b$
8b2o562b2o264bo440b$
573bo262b2o36b2o$
837b2o34bobo228b$
875bo265b$
434bobo704b$
434b2o35b3o667b$
435bo37bo264b$
472bo493b$
1000b3o227b$
1002bo264b$
1001bo265b$
1267b$
828b$
b2o5b2o1082b$
o2bo3bo2bo1118b$
bo2bobo2bo414bo704b$
4bobo415b2o36b2o667b$
2b3ob3o114b2o298b2o34bobo228b$
3o5b3o112b2o336bo491bo$
2o7b2o940b2o38b$
2o7b2o941b2o265b$
bob2ob2obo1246b$
b3o3b3o1246b$
2bo5bo1247b$
10bo5bo836b$
9b3o3b3o1060bobo$
9bob2ob2obo1060b2o38b$
8b2o7b2o392bobo665bo38b$
8b2o7b2o392b2o705b$
8b3o5b3o393bo302b$
10b3ob3o926b$
12bobo101b2o5b2o1082b$
9bo2bobo2bo97bo2bo3bo2bo1118b$
8bo2bo3bo2bo97bo2bobo2bo1119b$
9b2o5b2o101bobo1122b$
117b3ob3o114b2o565b$
115b3o5b3o112b2o829b$
115b2o7b2o980b$
115b2o7b2o980b$
116bob2ob2obo981b$
116b3o3b3o542b$
117bo5bo577b3o227b$
125bo5bo571bo262b2o$
124b3o3b3o569bo262bobo228b$
28b2o94bob2ob2obo834bo265b$
28b2o93b2o7b2o392bobo704b$
123b2o7b2o392b2o264bo440b$
16b2o105b3o5b3o393bo262b2o36b2o$
16b2o107b3ob3o659b2o34bobo228b$
127bobo101b2o5b2o589bo265b$
124bo2bobo2bo97bo2bo3bo2bo147bobo704b$
123bo2bo3bo2bo97bo2bobo2bo148b2o705b$
124b2o5b2o101bobo152bo302b$
232b3ob3o114b2o565b$
230b3o5b3o112b2o829b$
230b2o7b2o980b$
87b2o141b2o7b2o980b$
30bo3bo52b2o142bob2ob2obo981b$
30bo3bo196b3o3b3o542b$
232bo5bo806bo$
240bo5bo796b2o38b$
27b2obo3bob2o201b3o3b3o130bo665b2o37b$
28b3o3b3o43b3o3b3o54b2o94bob2ob2obo128b2o705b$
29bo5bo44bo2bobo2bo54b2o93b2o7b2o128b2o265b$
79bo3bobo3bo148b2o7b2o659b$
80bo2bobo2bo42b2o105b3o5b3o696b$
82bo3bo44b2o107b3ob3o926b$
80b2o5b2o153bobo101b2o5b2o855b$
79b3o5b3o149bo2bobo2bo97bo2bo3bo2bo147bobo704b$
79b3o5b3o148bo2bo3bo2bo97bo2bobo2bo148b2o705b$
239b2o5b2o101bobo152bo302b$
35b2o310b3ob3o114b2o565b$
35b2o308b3o5b3o112b2o602b$
345b2o7b2o9bobo704b$
80b3o119b2o141b2o7b2o9b2o264bo440b$
80b3o62bo3bo52b2o142bob2ob2obo11bo262b2o38b$
79b5o61bo3bo196b3o3b3o275b2o262bobo$
78b2o3b2o262bo5bo540b2o35b3o227b$
78b2o3b2o270bo5bo533bo37bo264b$
142b2obo3bob2o201b3o3b3o569bo265b$
143b3o3b3o43b3o3b3o54b2o94bob2ob2obo166b2o667b$
144bo5bo44bo2bobo2bo54b2o93b2o7b2o164bobo228b$
78b2o3b2o109bo3bobo3bo148b2o7b2o166bo262b3o227b$
78b2o3b2o2b2o106bo2bobo2bo42b2o105b3o5b3o431bo264b$
79b5o3b2o108bo3bo44b2o107b3ob3o432bo265b$
80b3o112b2o5b2o153bobo101b2o5b2o590b$
80b3o111b3o5b3o149bo2bobo2bo97bo2bo3bo2bo147bobo$
194b3o5b3o148bo2bo3bo2bo5bo91bo2bobo2bo148b2o35b3o227b$
354b2o5b2o7b2o92bobo152bo37bo262b2o$
150b2o217b2o91b3ob3o114b2o71bo262bobo228b$
150b2o308b3o5b3o112b2o336bo265b$
460b2o7b2o716b$
195b3o119b2o141b2o7b2o716b$
195b3o62bo3bo52b2o142bob2ob2obo314b$
194b5o61bo3bo196b3o3b3o542b$
193b2o3b2o262bo5bo580b$
193b2o3b2o270bo5bo572b$
257b2obo3bob2o201b3o3b3o130bo440b$
258b3o3b3o43b3o3b3o54b2o94bob2ob2obo128b2o38b$
259bo5bo44bo2bobo2bo54b2o93b2o7b2o128b2o265b$
193b2o3b2o109bo3bobo3bo148b2o7b2o429b3o227b$
193b2o3b2o2b2o106bo2bobo2bo42b2o105b3o5b3o431bo264b$
194b5o3b2o108bo3bo44b2o107b3ob3o432bo265b$
195b3o112b2o5b2o153bobo101b2o5b2o590b$
195b3o111b3o5b3o149bo2bobo2bo97bo2bo3bo2bo150b$
309b3o5b3o148bo2bo3bo2bo5bo91bo2bobo2bo185b3o227b$
469b2o5b2o7b2o92bobo190bo264b$
265b2o217b2o91b3ob3o114b2o71bo265b$
265b2o308b3o5b3o112b2o337b$
575b2o7b2o9bobo$
310b3o119b2o141b2o7b2o9b2o265b$
310b3o62bo3bo52b2o142bob2ob2obo11bo300b2o$
309b5o61bo3bo196b3o3b3o311bobo225bobo$
308b2o3b2o262bo5bo314bo225b2o38b$
308b2o3b2o270bo5bo533bo38b$
372b2obo3bob2o201b3o3b3o571b$
373b3o3b3o43b3o3b3o54b2o94bob2ob2obo168b$
374bo5bo44bo2bobo2bo54b2o93b2o7b2o395b$
308b2o3b2o109bo3bobo3bo148b2o7b2o432b$
308b2o3b2o2b2o106bo2bobo2bo42b2o105b3o5b3o432b$
309b5o3b2o108bo3bo44b2o107b3ob3o434b$
310b3o112b2o5b2o153bobo31b2o68b2o5b2o$
310b3o111b3o5b3o149bo2bobo2bo27bobo67bo2bo3bo2bo147bobo$
424b3o5b3o148bo2bo3bo2bo5bo22bo68bo2bobo2bo148b2o264bo$
584b2o5b2o7b2o92bobo152bo262b2o38b$
380b2o217b2o91b3ob3o114b2o298b2o37b$
380b2o308b3o5b3o112b2o337b$
690b2o7b2o12b$
425b3o119b2o141b2o7b2o276b$
425b3o62bo3bo52b2o142bob2ob2obo314b$
424b5o61bo3bo196b3o3b3o314b$
423b2o3b2o262bo5bo315b$
423b2o3b2o270bo5bo$
487b2obo3bob2o201b3o3b3o131b$
488b3o3b3o43b3o3b3o54b2o94bob2ob2obo166b2o$
489bo5bo44bo2bobo2bo54b2o93b2o7b2o164bobo228b$
423b2o3b2o109bo3bobo3bo148b2o7b2o166bo265b$
423b2o3b2o2b2o106bo2bobo2bo42b2o105b3o5b3o432b$
424b5o3b2o108bo3bo44b2o107b3ob3o434b$
425b3o112b2o5b2o153bobo101b2o5b2o$
425b3o111b3o5b3o149bo2bobo2bo97bo2bo3bo2bo150b$
539b3o5b3o148bo2bo3bo2bo97bo2bobo2bo188b$
699b2o5b2o101bobo191b$
495b2o310b3ob3o114b2o73b$
495b2o308b3o5b3o112b2o$
805b2o7b2o12b$
540b3o119b2o141b2o7b2o46b3o227b$
540b3o62bo3bo52b2o142bob2ob2obo49bo264b$
539b5o61bo3bo196b3o3b3o48bo265b$
538b2o3b2o262bo5bo315b$
538b2o3b2o270bo5bo$
602b2obo3bob2o201b3o3b3o131b$
603b3o3b3o43b3o3b3o54b2o94bob2ob2obo168b$
604bo5bo44bo2bobo2bo54b2o93b2o7b2o167b$
538b2o3b2o109bo3bobo3bo148b2o7b2o167b$
538b2o3b2o2b2o106bo2bobo2bo42b2o105b3o5b3o$
539b5o3b2o108bo3bo44b2o107b3ob3o$
540b3o112b2o5b2o153bobo31b2o68b2o5b2o$
540b3o111b3o5b3o149bo2bobo2bo27bobo67bo2bo3bo2bo150b$
654b3o5b3o148bo2bo3bo2bo5bo22bo68bo2bobo2bo188b$
814b2o5b2o7b2o92bobo191b$
610b2o217b2o91b3ob3o114b2o73b$
610b2o308b3o5b3o112b2o$
920b2o7b2o12b$
655b3o119b2o141b2o7b2o46b3o$
655b3o62bo3bo52b2o142bob2ob2obo49bo$
654b5o61bo3bo196b3o3b3o48bo$
653b2o3b2o262bo5bo$
653b2o3b2o270bo5bo$
717b2obo3bob2o111b3o87b3o3b3o131b$
718b3o3b3o43b3o3b3o54b2o6bo87bob2ob2obo168b$
719bo5bo44bo2bobo2bo54b2o5bo87b2o7b2o167b$
653b2o3b2o109bo3bobo3bo148b2o7b2o167b$
653b2o3b2o2b2o106bo2bobo2bo42b2o105b3o5b3o$
654b5o3b2o108bo3bo44b2o107b3ob3o$
655b3o112b2o5b2o153bobo101b2o5b2o$
655b3o111b3o5b3o149bo2bobo2bo97bo2bo3bo2bo$
769b3o5b3o148bo2bo3bo2bo97bo2bobo2bo$
929b2o5b2o101bobo$
725b2o310b3ob3o$
725b2o308b3o5b3o$
1035b2o7b2o12b$
770b3o119b2o141b2o7b2o49b$
770b3o62bo3bo52b2o142bob2ob2obo50b$
769b5o61bo3bo196b3o3b3o50b$
768b2o3b2o262bo5bo$
768b2o3b2o270bo5bo$
832b2obo3bob2o201b3o3b3o$
833b3o3b3o43b3o3b3o54b2o94bob2ob2obo$
834bo5bo44bo2bobo2bo54b2o93b2o7b2o$
768b2o3b2o109bo3bobo3bo148b2o7b2o$
768b2o3b2o2b2o106bo2bobo2bo42b2o105b3o5b3o$
769b5o3b2o108bo3bo44b2o107b3ob3o$
770b3o112b2o5b2o153bobo33b$
770b3o111b3o5b3o149bo2bobo2bo30b$
884b3o5b3o148bo2bo3bo2bo29b$
1044b2o5b2o9b$
840b2o220b$
840b2o2$
885b3o119b2o$
885b3o62bo3bo52b2o$
884b5o61bo3bo$
883b2o3b2o$
883b2o3b2o$
947b2obo3bob2o114b$
948b3o3b3o43b3o3b3o54b2o7b$
949bo5bo44bo2bobo2bo54b2o7b$
883b2o3b2o109bo3bobo3bo$
883b2o3b2o2b2o106bo2bobo2bo42b2o$
884b5o3b2o108bo3bo44b2o$
885b3o112b2o5b2o$
885b3o111b3o5b3o$
999b3o5b3o2$
955b2o$
955b2o2$
1000b3o119b2o$
1000b3o62bo3bo52b2o$
999b5o61bo3bo$
998b2o3b2o$
998b2o3b2o$
1062b2obo3bob2o$
1063b3o3b3o43b3o3b3o$
1064bo5bo44bo2bobo2bo$
998b2o3b2o109bo3bobo3bo$
998b2o3b2o2b2o106bo2bobo2bo$
999b5o3b2o108bo3bo$
1000b3o112b2o5b2o$
1000b3o111b3o5b3o$
1114b3o5b3o2$
1070b2o$
1070b2o2$
1115b3o$
1115b3o$
1114b5o$
1113b2o3b2o$
1113b2o3b2o4$
1113b2o3b2o$
1113b2o3b2o2b2o$
1114b5o3b2o$
1115b3o$
1115b3o$
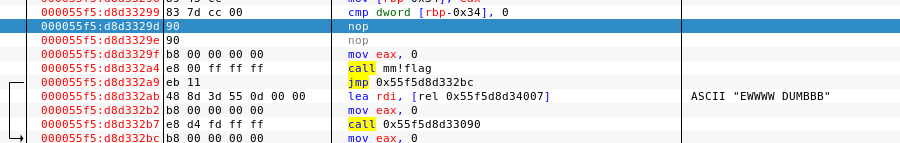
!A quick google search I find that the RLEextension is related to Run Length Encoded Bitmaps.
Further searching I find that there is a tool called “Golly” for viewing RLE files.
I let the online webapp load and then open my golly.rle file in it:

That gives me the flag in a scrolling marquis-type display:
UDCTF{th3y_c4ll_thems3lves_the_fl4g_smash3rs}This was a pretty unique challenge.