This is from the 2021 Vishwa CTF
For this challenge, we are given a cryptic hint:

A quick Google search tells me that Reddit is the front page of the internet, so I search for entries related to vishwactf on reddit:

I see that there is a comment indicating that another comment has been deleted:

AI hop in my time machine at Archive.org and go down memory lane:

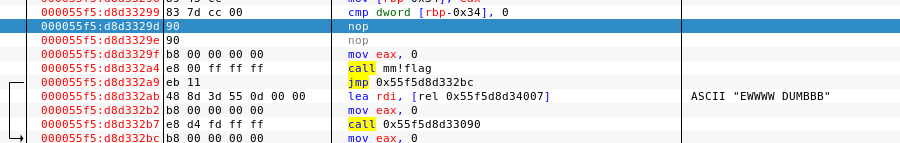
I now have what appears to be a ciphered flag with a clue. The part about the “18th century French scholars” tells me to try decrypting it as a Vigenere cipher. I head over to dcode.fr and try it out. The automatic decryption failed, so after some contemplating, I try “VISHWACTF” as the key and I get the flag:

And yes, OSINT is overlooked!